By Lawrence Tan
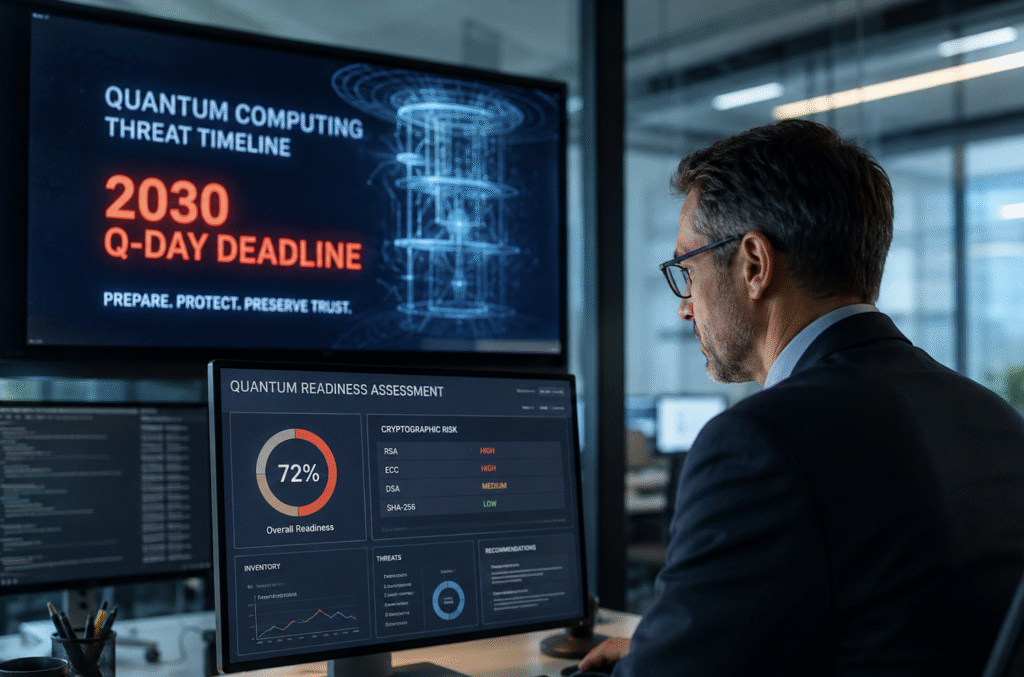
In much of today’s quantum conversations, one question tends to dominate: When will quantum computers become powerful enough to break the cryptography that underpins today’s digital world? It’s an important question, but not the only one that matters. Today, organisations should be asking a more practical question: Are they prepared for the transition that is already on its way?
Post-quantum cryptography is no longer just a hypothetical, future-facing research topic. It is a business issue tied to digital trust, operational resilience and long-term risk management. Organisations that handle sensitive data cannot afford to wait for a definitive quantum milestone. They need to start building the visibility, control and crypto-agility to move with confidence.
The real gap is between awareness and action
If there is one theme that stands out today, it’s this: awareness of the quantum threat is rising faster than enterprise readiness.
The Entrust 2026 Global State of Post-Quantum and Cryptographic Security Trends report found that only 38 per cent of organisations globally, and 33 per cent in Singapore, are actively transitioning to post-quantum cryptography.
In Singapore, only 43 per cent report full visibility into certificates across the enterprise, while 62 per cent say managing cryptographic assets is extremely or very difficult. At the same time, around half of Singaporean cybersecurity practitioners believe a quantum computer capable of breaking RSA and ECC could emerge within five years.
That disconnect matters: many organisations understand the threat in principle, but still underestimate the scale of the transformation required to respond. Post-quantum migration is not a simple algorithm swap – it affects certificates, keys, secrets, hardware, policies, partner ecosystems and legacy infrastructure – and for most organisations, transitioning all of that across complex environments will take years, not months.
The threat is no longer future tense
One of the biggest misconceptions about the quantum threat is that organisations can afford to wait until a cryptographically relevant quantum computer arrives or until standards and vendor solutions are fully post‑quantum ready, and react accordingly.
The reality is that they cannot wait. Adversaries are already pursuing “harvest now, decrypt later” tactics: collecting encrypted data today with the intention of decrypting it in the future once the right quantum capabilities become viable. That means data with a long shelf life, such as financial records, health information, intellectual property, government records and critical infrastructure data, may already be at risk, even if today’s encryption has not yet been broken in real time.
This is why post-quantum readiness should not be treated as a countdown to a single event. It is a multi-year cryptographic transformation journey, and organisations that delay may find that the window to prepare has narrowed far faster than expected.
Visibility is where quantum readiness begins
The starting point is not choosing new algorithms; it is knowing where cryptography exists across the enterprise in the first place. That means understanding which systems, applications, certificates, keys and secrets rely on vulnerable algorithms, what data they protect, how they are governed, and where the greatest exposures lie. Without that visibility, organisations cannot prioritise migration, automate lifecycle management, enforce policy consistently or build a credible roadmap forward.
Many organisations are still struggling with this. When cryptographic assets are distributed across hybrid environments, embedded in legacy systems, or managed inconsistently across teams, the result is a fragmented security posture. And without visibility, there is no real foundation for crypto-agility.
A confident transition requires more than planning
Once organisations have visibility into their cryptographic assets, the next step is turning that insight into a practical migration strategy. In most environments, that means focusing on a handful of foundational capabilities that make post-quantum readiness achievable in practice, not just in principle.
First, organisations need discovery and inventory. Teams must be able to identify and classify cryptographic assets across the environment – from certificates and keys to secrets and encrypted workloads – and understand where they sit, what they protect and who owns them.
Increasingly, this level of visibility is also becoming essential to both regulatory compliance and operational resilience. Across markets, regulators are placing greater emphasis on how organisations identify, govern and secure the technologies, and dependencies that underpin digital trust – from Singapore’s MAS Technology Risk Management Guidelines and Bank Negara Malaysia’s Risk Management in Technology framework, to Australia’s Cyber Security Act 2024. In practice, that makes cryptographic visibility a foundation for both compliance and resilience. A Cryptographic Bill of Materials can support this by giving organisations a clearer view of where cryptography is used, how it is managed, and where potential risks may sit across the enterprise.
Second, they need governance and policy control. Once those assets are visible, organisations need a consistent way to assess risk, assign ownership, enforce standards and respond as requirements change. Without that layer of control, visibility alone does not translate into action.
Third, they need automation. With certificate lifecycles shrinking and cryptographic environments growing more complex, manual processes are no longer sustainable. Public trust certificate validity windows are being reduced from 398 days to 200, then 100, and ultimately down to 47 days by 2029. That alone should be enough to show why lifecycle management, renewal automation and policy-driven controls are now essential.
Fourth, they need crypto-agility. It is not enough to prepare for one future migration. Organisations need the ability to adapt cryptographic policies, algorithms and infrastructure over time without having to re-engineer their environments from scratch. In practice, that means reducing dependence on hard-coded cryptography, building more flexible certificate and key management processes, and ensuring systems can support change. This flexibility will be critical not only as quantum-safe standards mature, but as compliance expectations, risk profiles and ecosystem dependencies continue to evolve.
And finally, they need quantum-safe infrastructure they can build on. That includes the ability to secure and manage cryptographic assets at scale, automate certificate lifecycle operations, strengthen PKI and key management, and support a transition path that is both hybrid-ready and future-ready.
Quantum readiness cannot wait: The next step is moving from planning to execution
The organisations that will navigate this transition most effectively are not those waiting for perfect certainty. They are the ones investing now in the visibility, automation and quantum-ready foundations that allow them to move from planning to implementation.
For Singapore, this is especially relevant. The market is already laying groundwork for quantum-safe migration through the Cyber Security Agency’s Quantum-Safe Handbook and Quantum Readiness Index. In this highly connected economy, organisations cannot assume global regulatory shifts or ecosystem changes will remain external pressures for long.
The most important message for organisations today is not to predict exactly when quantum computers will become a real-world threat, but to ensure the foundations for post-quantum resilience are already being built.
The regulatory direction is clear, the quantum timeline is accelerating, and the cryptographic visibility and management tools are already available. Such platforms can help organisations gain visibility into cryptographic assets, strengthen lifecycle management, and move from awareness to execution with confidence.
Organisations that act early will be better positioned to protect long-lived data, preserve digital trust, and control the pace of their post-quantum transition. Those that delay may discover that the greatest risk was never a lack of awareness, but a lack of readiness when action inevitably becomes unavoidable.